Passwords are hard work. We can’t use simple passwords, because they’ll be easy to guess or brute force. We can’t reuse passwords, because when a random Internet forum’s database is compromised, we don’t want anyone to use that data to steal our Slashdot, Reddit, or bank account. What should we do?
I’ll be surprised if you’re not already using a password manager. You’re probably using something like 1Password or LastPass to store your passwords. Maybe you’re an old man like me, and you’re still using KeePass. It almost doesn’t matter what you use. You need to be using something, right?
- One Month with Bitwarden at patshead.com
- Bitwarden
- LastPass
What have Pat and Brian been up to lately? To find out you can check out the latest episodes of The Butter, What?! Show
My life up until today
I’ve been using KeePass for a long, long time. I couldn’t even take an educated guess about when I started using it. The only change I made was to upgrade to KeePass2 at some point. Even that was a long time ago!
KeePass is an encrypted password database. Your password database is stored locally, and KeePass has a crufty but usable interface that lets you keep track of usernames, passwords, and URLs. There are plugins to integrate KeePass2 with various web browsers, and it has the ability to automatically type your username and password into various dialog boxes.
Syncing your database between your devices is a problem you have to solve on your own. I store my KeePass database file in an encrypted Seafile library. That keeps the database in sync on my desktop, laptop, and tablet. The Android Seafile client doesn’t actually sync files, so I use SyncThing to keep the database on my phone up to date.
The storage devices on my desktop, laptop, tablet, and phone are all encrypted. The KeePass database is encrypted. My Seafile library is encrypted. There’s encryption all over the place, and for the most part, the database doesn’t leave my control. I don’t own my Seafile server, though.
- One Month with Bitwarden at patshead.com
- Bitwarden
- Outsourcing My Self-Hosted Cloud Storage at patshead.com
- LastPass
What’s the problem?
All this stuff works fine. All these layers of encryption are nice. KeePass’s integration with Chrome and Firefox works just fine. Getting sync going was easy, but required a bit of effort syncing to Android. Once I had it set up, it worked just fine. Why not keep using KeePass?
To tell you the truth, I probably would have kept using KeePass for years. Last week, I saw Bitwarden mentioned in a comment thread somewhere. I didn’t think much of it. I just assumed it was another attempt at a KeePass replacement.
Then I saw it mentioned again a few days ago, and I realized that Bitwarden is attempting to be a replacement for LastPass or 1Password. That piqued my interest. An open source LastPass equivalent that I could host myself sounds awesome!
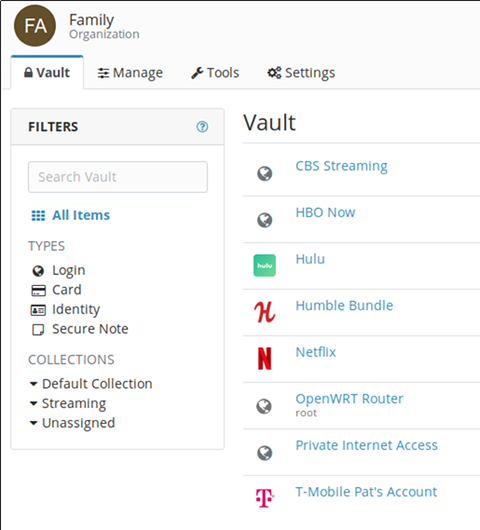
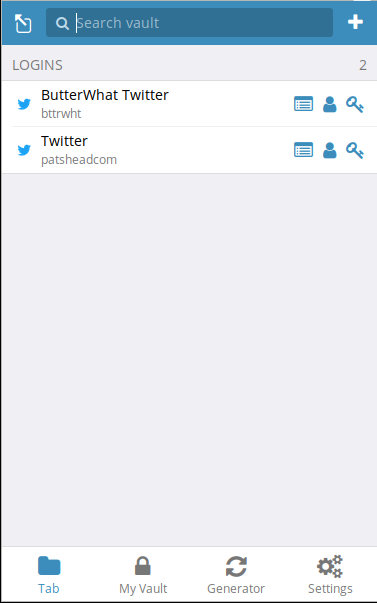
1Password and LastPass have one particular feature that KeePass will never be able to have. They allow you to share passwords with your friends and family. This wasn’t a deal breaker for me, but I imagine it will come in handy. With Bitwarden, our Netflix and Hulu passwords won’t get out or sync between mine and my wife’s KeePass databases!
- One Month with Bitwarden at patshead.com
- Bitwarden
- LastPass
I’m using Bitwarden, but I’m not hosting my own server
A few nights ago, I did a bit of research on Bitwarden. I’ll tell you some of the details of my findings soon, but I didn’t find anything that scared me away. I signed up for an account, upgraded to a premium account for $10 per year, and I imported my KeePass2 database.
The process was painless, and I haven’t had any problems signing into anything yet. I’ll keep you updated over the next few months.
You can host your own Bitwarden service, and it looks easy enough to set up. If you already have a server out there somewhere, they offer a Docker image that you should be able to have up and running in no time.
When I had a server colocated downtown, I would most definitely have set this up. I’ve been trying to offload most of that work to other companies, though, and this is definitely inexpensive enough to outsource.
The free Bitwarden account would meet my needs, but the premium account was inexpensive enough.
- One Month with Bitwarden at patshead.com
- Bitwarden
- LastPass
Password hygiene and vault health reports
These services are available with a premium Bitwarden account, but what on Earth does that mean?! Bitwarden will correlate information in your password vault with leaked password databases. Have your email addresses been compromised in a password leak? Are you using passwords that are commonly found in those leaked databases? Are you still using weak passwords anywhere?
Bitwarden can give you this information. I have a lot of old cruft in my KeePass database. Ancient websites that I will probably never log into again. Websites that are long gone. Old garbage. Bitwarden’s health service threw up a lot of red flags on that old junk!
- One Month with Bitwarden at patshead.com
- Bitwarden
- LastPass
KeePass is better in many important ways
BitWarden will always be a little scary. Just like 1Password and LastPass, the BitWarden browser extension has full access to your password vault. Once you enter your passphrase, all that important information is sitting around in memory in an unencrypted state. Not only that, but that unencrypted data is part of your Chrome or Firefox browser process.
You’re relying on Firefox or Chrome to keep malicious web pages or extensions out of your password vault. You could be one compromise away from your password database being gobbled up.
KeePass is always a separate process. The browser extensions for KeePass don’t store your data. They communicate with a KeePass process to request a particular username and password. When the request is made, the KeePass desktop app will ask you for confirmation.
If you’re logging into Reddit, you might check the button to remember this decision. Next time you log in, KeePass will hand that password over to the browser without prompting. Maybe you would want to be more careful with your bank password, so you might require confirmation each time.
I know I’m oversimplifying things when I say this, but I’m trying to keep this post under 2,000 words. Bitwarden, 1Password, and LastPass may have your bank password in memory in the browser process whenever the vault is unlocked.
KeePass may have the password in memory, but it is further protected from the browser by your operating system’s kernel’s memory protections. That’s a much bigger wall to break down or climb over, and just having an additional wall is nice.
- One Month with Bitwarden at patshead.com
- Bitwarden
- LastPass
Does this really matter?
It depends who you ask. Security and ease of use are almost always at odds. It would be simplest to just use a password everywhere for your password, but that wouldn’t be safe. It would be extremely safe if you could memorize a different 128-character password for every single service that you use, and type it in manually each time, but that’s never going to happen.
I’ve thought about this problem for years. I’ve done my research. I’ve decided that the level of protection and convenience provided by Bitwarden, LastPass, or 1Password is the right compromise for me.
Yes. I most definitely gave up some amount of security for the sake of convenience when I switched from KeePass to Bitwarden. I’m pleased with this compromise.
- One Month with Bitwarden at patshead.com
- Bitwarden
Bitwarden’s pricing structure is weird
I was confused when I looked at their pricing charts. I quickly zeroed in on the $1/month family plan listed under organization accounts. It says it includes 5 users, and that’s only $2 more per year than the premium plan. Seems like a no-brainer, right?
That’s not how it works. Organization accounts are something completely different. Each user has to have either a free or a premium account. The organization accounts are where the shared password vaults live.
I have a premium account. My wife has a free account. I believe you could say we’re using a separate organizational account for the passwords we share with our family. It is just the two of us, so our organizational account is free as well. We will likely be setting up an organizational account for Butter, What?! to make it easier to share important passwords with Brian.
- One Month with Bitwarden at patshead.com
- Bitwarden
- LastPass
Is Bitwarden safe?
I suppose it depends on what you’re trying to protect yourself from and your definition of safe, but I believe it is more than safe enough for my use. I did some research. I tried to find as much terrifying information about Bitwarden as I could. The scariest stuff isn’t that scary.
I found this short security review of Bitwarden. He found that the password to log into the service and the password used to encrypt your database are the same. He has a heading that says your password is sent to the server, but it appears that some sort of salted hash is actually sent to the server.
That’s not too terrible. It would be nice if two different passwords could be used, but I understand the design choice. A single password is much more convenient for the user!
He also noted that Bitwarden loads quite a bit of Javascript from third-party sources. It seems that this has been addressed to some extent by the Bitwarden developer in recent months.
Bitwarden was audited by a third-party security company last year. There were definitely some problems. The major ones seem to have been addressed quite quickly.
- One Month with Bitwarden at patshead.com
- Bitwarden
- Results of Bitwarden security audit at Reddit
- A short security review of Bitwarden at electricmonk.nl
Conclusion
I’ve only been using Bitwarden for a few days. I’ve been holding off on migrating from KeePass to something like LastPass, because I prefer to use open-source software. I especially prefer to use open source software for my most important infrastructure. My virtualization, my web servers, my file sync server, and all my computers run on open-source software.
Bitwarden has been a welcome surprise, and I look forward to giving you an update in a few months. I expect that there won’t be much to tell you about. If it is working fine today, I expect it to continue to do so in three months!
What do you think? Are you a KeePass holdout like me, or have you already moved on to something like LastPass or 1Password? Did you already discover Bitwarden long before I heard of it? Tell me about your experiences in the comments, or stop by the Butter, What?! Discord server to chat with us about it!
- One Month with Bitwarden at patshead.com
- Bitwarden
- Results of Bitwarden security audit at Reddit
- A short security review of Bitwarden at electricmonk.nl
- Outsourcing My Self-Hosted Cloud Storage at patshead.com
- LastPass
